A combined effort by international authorities, including the Australian Federal Police, has disrupted the operations of two prolific infostealers used to take millions of credentials and bank account details.

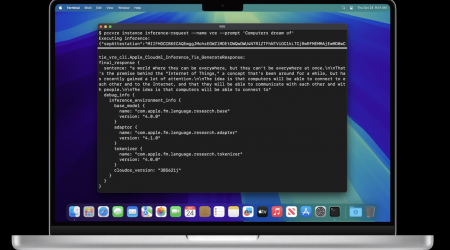
US authorities said they were worked with Operation Magnus, where law enforcement agencies worldwide investigated the RedLine and META Infostealers.
Infostealers are a type of malware that users are tricked into downloading, which then steals data from their machines.
The data is typically then sold on cybercrime forums, where it can be used “for further fraudulent activity and other hacks,” the US Attorney’s Office for the Western District of Texas said in a statement.
RedLine had been used “to conduct intrusions against major corporations,” the office said, adding that infostealers enabled threat actors to “bypass multi-factor authentication through the theft of authentication cookies and other system information.”
Both RedLine and META are sold as malware-as-a-service, where affiliates can buy a license and then use it to launch a campaign.
The US said it had identified “millions of unique credentials (usernames and passwords), email addresses, bank accounts, cryptocurrency addresses, credit card numbers, etc” so far, though this number could increase.
Authorities seized two domains used by RedLine and META for command and control.
An alleged developer and administrator of Redline is also facing several charges.
The Australian Federal Police briefly highlighted its role in the investigation in a LinkedIn post on Thursday.
“The AFP has supported its international partners in a major operation to disrupt infostealer malware called RedLine and META,” it said.
“The collaborative investigation involved law enforcement agencies from the Netherlands, Belgium, United States, UK, Portugal and Australia.
“Further investigations into the global operation are ongoing.”
Cyber threat intelligence firm Intel471 said in a blog post that the operation against the Redline and META infostealers “struck at … core infrastructure and communication channels, but as of October 30, RedLine activity has only slightly decreased.”
“The likely reason is that RedLine’s code and administration panel software is sold by other underground vendors outside of the core operation that was targeted by law enforcement,” Intel471 surmised.
“Also, the malware and panel administration software has been cracked, or had its licensing protections circumvented, allowing threat actors to use it via alternate channels.
“This means some RedLine operators have been unaffected by this action and are working as usual.”
Still, Intel471 said the disruption effort was significant.
“The action has successfully disrupted two significant strains in the infostealer ecosystem,” Intel471 said.
“The back-end data from the systems should help in remediation, as it should be possible to identify and alert victims … [and] may also help in identifying key threat actor customers of these malware programs.
“There’s also the psychological effect on threat actors.”